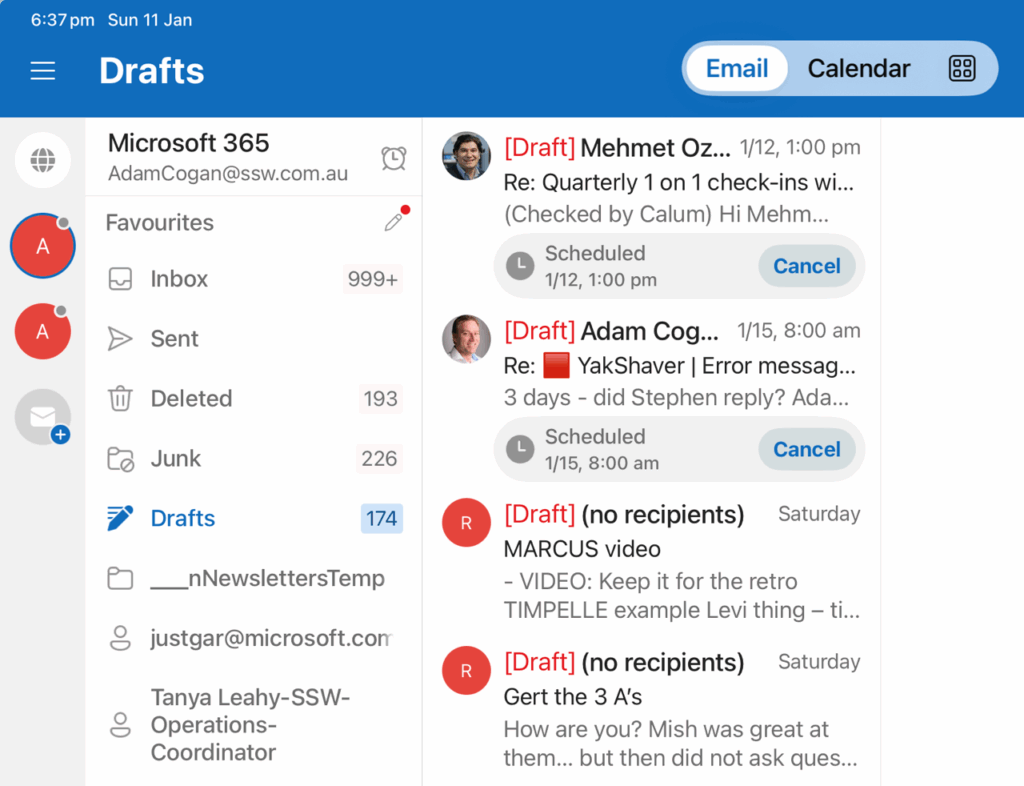
Delayed emails get saved in Drafts. Those emails should be separate from real draft emails because they are unfinished emails.
Could you save it in a subfolder eg. Drafts\Delayed
A common UI thing is to use > and <
Microsoft dialogs often use:
So I would change:
To:
And change:
To:
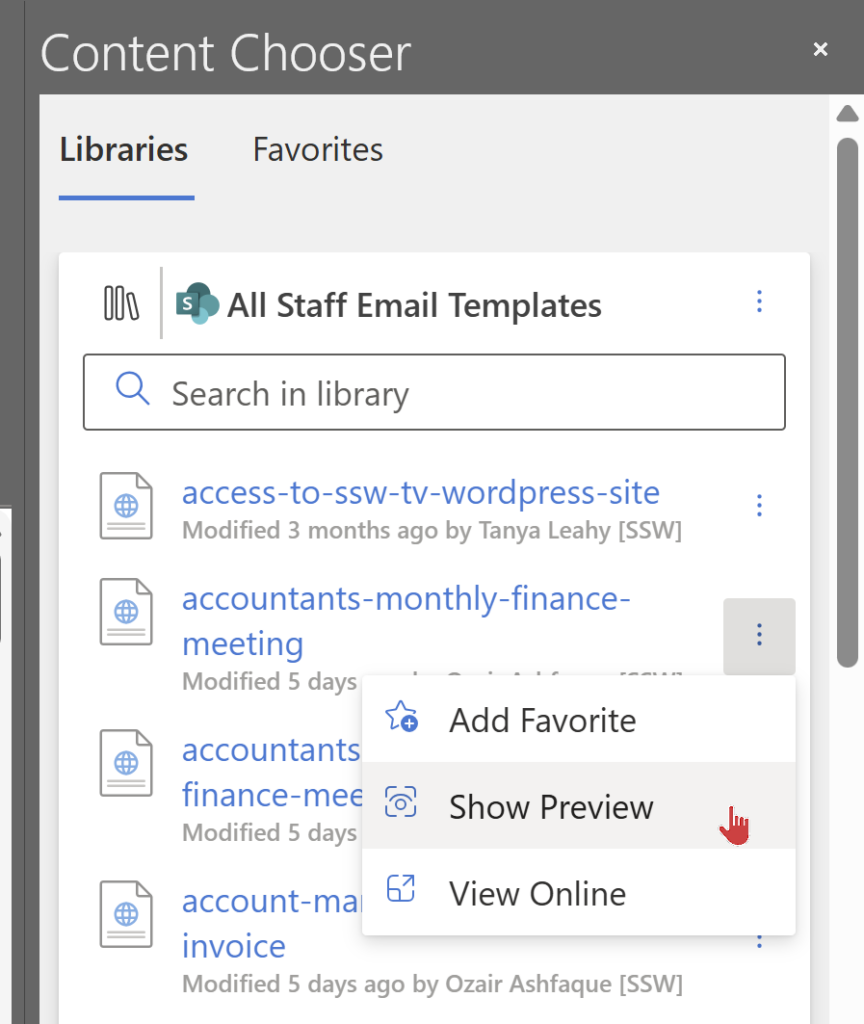
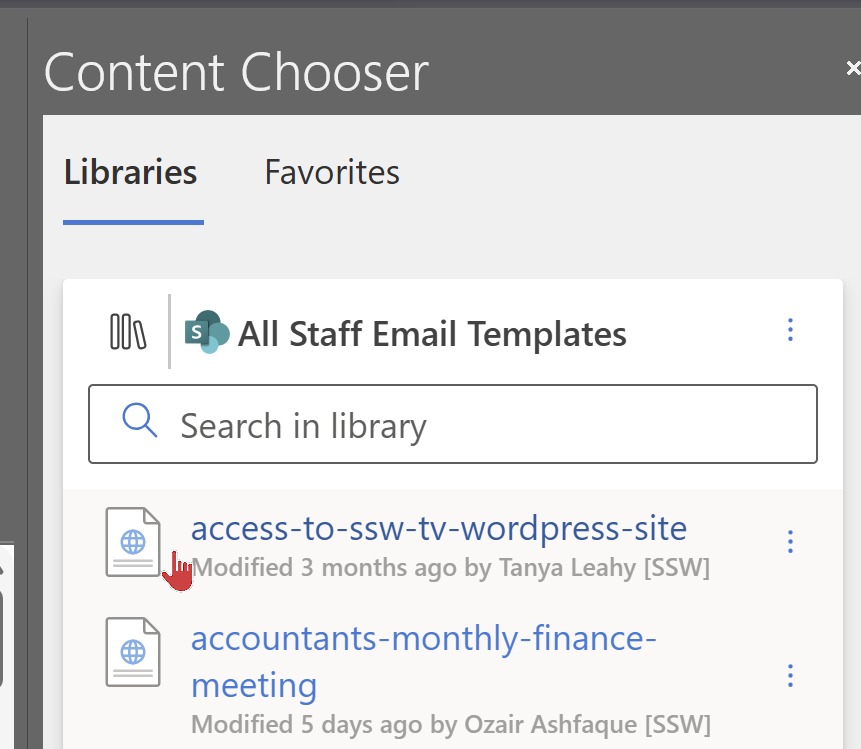
Also I would make it easier to preview to avoid needing to click the 3 dots…
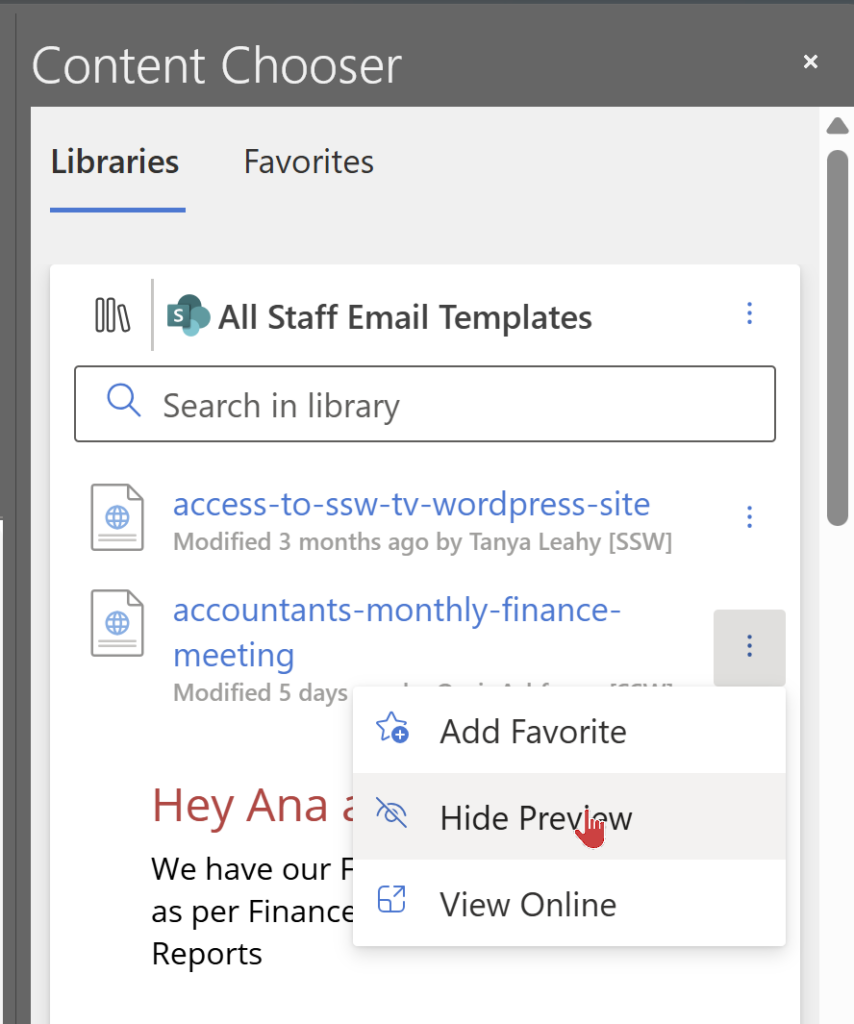
See the red mouse, after 2 seconds of waiting I would show an option “Show Preview…”
…which would popup open a new window with the preview
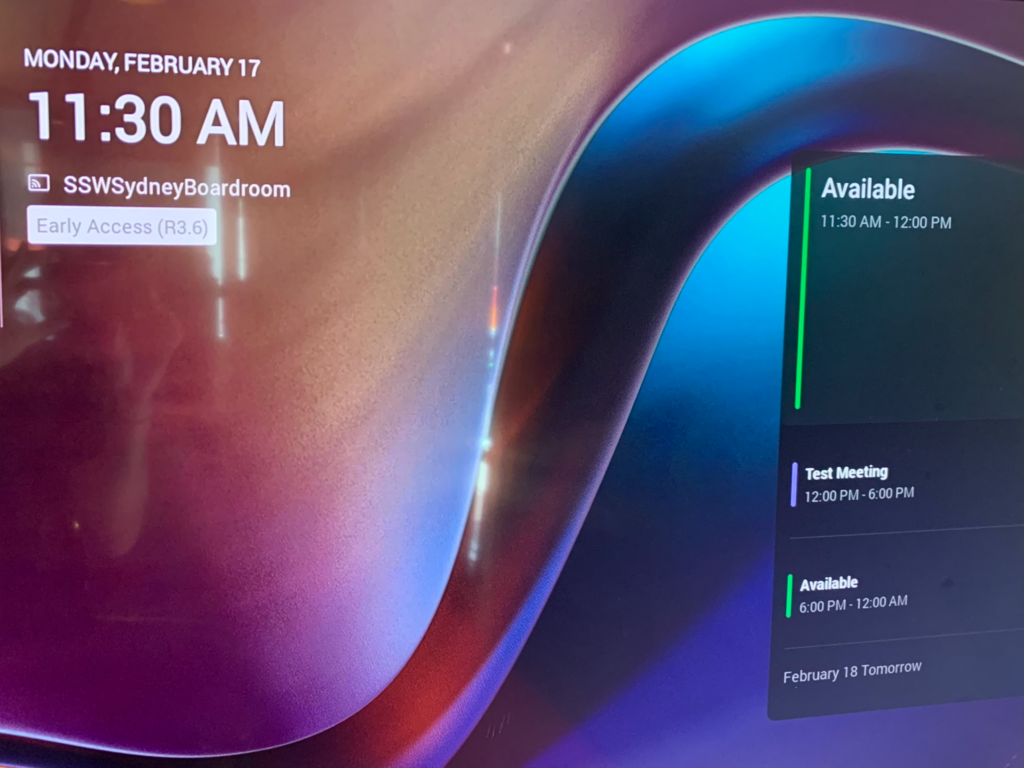
Microsoft Teams Rooms devices have a useful standby screen, showing a calendar of upcoming meetings for the room.
However, the visual hierarchy does not make it clear how long each booking is for, or how much available time there is before the next meeting starts. While it makes sense to highlight the current time period, the size of the boxes should match the periods of each booking. This would be consistent with other calendars, e.g. Outlook.
Suggestion:
– Change the calendar boxes to match the time period of each booking/availability
– Add a time period next to each title, e.g. change from Available to Available (30 mins).
SysAdmins find it a lot of work maintaining permissions to resources like Azure.
Both Devs and SysAdmins love Identity Governance and in particular Access packages as resources are now more secure and quicker for to grant access to.
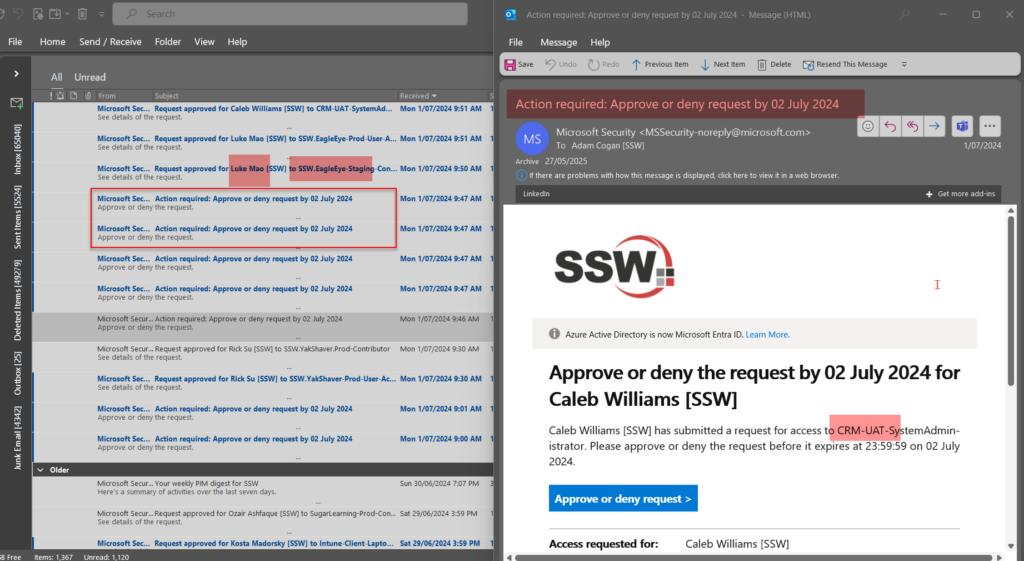
❌ Access Package requests do not show the product or user in the email subject. If subjects contained the same details it would be easier to quickly see who is requesting lots of access on a regular basis.
Suggestion:
Replying to an Issue via email is a great feature as it saves you opening GitHub – you can reply without leaving Outlook.
The problem is the messages will include a lot of noise (sometimes blank spaces) with the email history and irrelevant data, which makes them hard to follow in GitHub…
Suggestion: Clean up email replies by keeping only the body of an email (no history, no extras)
See the replies in this Issue that were sent via email: https://github.com/SSWConsulting/SSW.People/issues/507#issuecomment-1692676860

Related links:
Update: Microsoft have fixed this bug in June 2024
When you are in Teams looking at a webpage often you want to open it in the browser. E.g, Loop pages. Recently it started giving: “The link has been removed.”
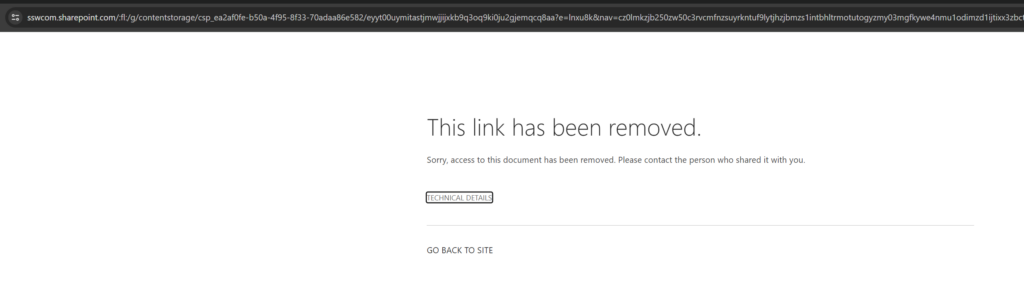
After very careful inspection in Teams I realized that the URL was being changed when I clicked on the ‘open in browser’ button to all lowercase. This breaks any sharing links to things like SharePoint as they are case-sensitive.
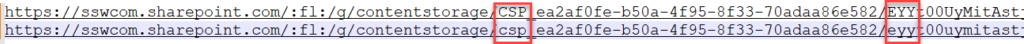
URL’s by nature are case-sensitive and should not be changed
We are nearly complete on an AI solution – it is being built on top of Microsoft Teams and Azure OpenAI APIs. We call it SSW YakShaver.
The product has a blocking issue. We are recording a Teams call (and screen) and we have hit something called a “compliance policy”.
The below is what we plan to do from here. I would have assumed we would have gone with Option 1 (using the Teams bot with a compliance policy) but it seems like we are going to use the Graph API (simpler).
Thoughts?
——————————————————————————————————————-
I got this email from the YakShaver team:
We have been trying to get the compliance policy working in MS Teams (Option1), but have pretty much given up.
We have decided to do Option 2 below followed by Option 2.1.
We are *not* doing Option 1.
Here are all the points we have learnt.
Then the user flow.
Then the pros and cons.
Using a Teams bot with a compliance policy to record the audio and video, it will record every participants sound individually, those who are not in the policy will not be recorded.
Using the Graph API to do the work, the user manually start and stop recording, and then the YakShaver will get the transcrips for the user manually.
Use communication service to automate the call record process – need a POC after Graph is done.
– It’s easy to use
– We can get rid of the compliance policy which is much much simpler!!!!!
– I can see the potential of making YakShaver into a commercial project.
– We can define our own compliance rule rather than rely on Azure to set up the compliance policy
– Calls have to be initialized from communication services
– It’s our responsibility to notify recording – very important
– We have to do compliance recording policy ourselves if we make it commercial later – might need a lawyer
Things we are sure of from the documentation:
We have built a cool reporting tool www.sswEagleEye.com that uses the Microsoft Graph API to produce insights into employees’ email data.
However, when an employee leaves the company, we are no longer able to access that former employee’s email messages. This makes sense normally, but not in our scenario.
We need former employees’ email data or we have incomplete and potentially misleading reports.
Suggestion:
Microsoft Graph API should provide a method to access former employees’ email data, either through a dedicated endpoint or by incorporating a flag or parameter in the existing API requests.
At SSW we really love using Microsoft Loop to collaborate with each other. We think it would make a great replacement for OneNote in Teams for project Wikis and other important collaboration documents.
⚠️ However, the loop files are stored inconsistently (some are in your workspace and some are in OneDrive and some end up in the Microsoft Team if you create it in the chat), so I worry about data loss.

Loop pages created in Microsoft Loop can have their link copied to a Team but can’t be shared to a Team. The storage for these loop files then stays with the creator’s workspace. When a creator leaves the company, the link is broken.
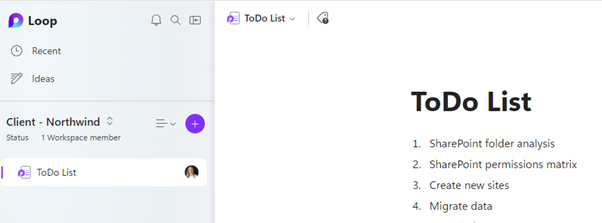
You can add a Loop component to a Teams post and that creates a .loop file in the Teams storage, which is great, but you can only add 1 component per post. You then must pin the post to the top so that other Team members can find it.


As a workaround, you can add a Teams OneNote, then add the loop components inside OneNote. However that doesn’t work as then strangely the files are stored under the creator’s OneDrive not in the Teams storage.

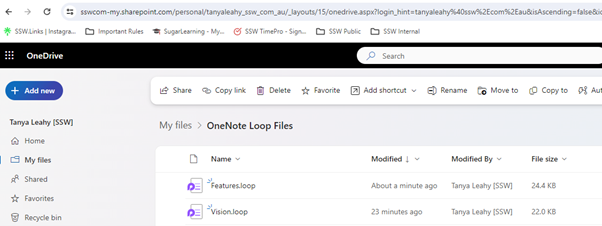
This storage behaviour is not consistent, and it is not ready for enterprises (as they will lose data in Loops).